
How AI software will change architecture and design
AI text-to-image software like Midjourney, DALL-E and Stable Diffusion has the potential to change the way that architects approach the creation and concept stages of

AI text-to-image software like Midjourney, DALL-E and Stable Diffusion has the potential to change the way that architects approach the creation and concept stages of

This post elaborates on various factors that go into consideration while prioritizing various AI initiatives. Data lies at the core of all business strategies. It

The buzz around generative AI today is deafening. Generative AI refers to artificial intelligence that can generate novel content, rather than simply analyzing or acting

Can Big Data bring BIG changes in the recruitment sector? Let’s find out in this article! There’s no doubt that the success of any company
Some of the world’s most advanced artificial intelligence (AI) systems, at least the ones the public hear about, are famous for beating human players at

If data isn’t managed well, your organization could be at significant risk. This list will help you spot areas where your data governance may fall

AI is everywhere—at least from a high-level perspective. But does it belong in your business? That depends. There’s little argument that AI offers companies plenty

To attain true AI understanding, researchers should shift their attention to developing a basic, underlying AGI technology that replicates the contextual understanding of humans. Industry

From the minute an entrepreneur has an idea for a business, the story is written by data and decisions based on it. Data shows whether

The face of data within an organisation has expanded over the years and continues to evolve rapidly. Almost certainly, you’ll recognise that where data is
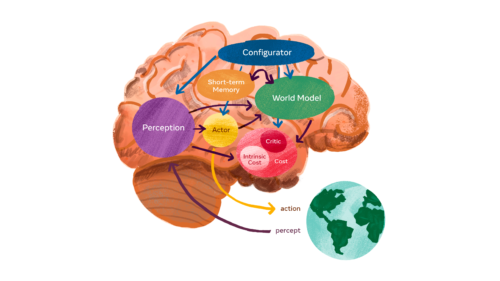
For all the remarkable recent progress in AI research, we are still very far from creating machines that think and learn as well as people

Even with the growing awareness about cybersecurity, many myths about it are prevalent. These misconceptions can be a barrier to effective security. The first step
