Why Enterprise Artificial Intelligence Needs Humans in the Loop
In the aftermath of the Pegasus Spyware software revelation there were calls from all sectors of society for vendors to better regulate and control their
In the aftermath of the Pegasus Spyware software revelation there were calls from all sectors of society for vendors to better regulate and control their

Adding levels of cybersecurity to a mobile computing environment using traditional methods can often be a matter of making trade-offs between taking the necessary security
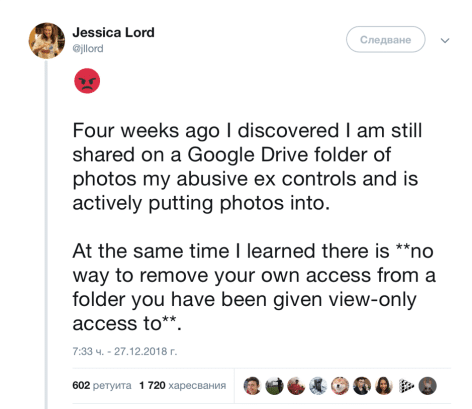
A shows that 35% of women, worldwide, have experienced violence, and 39% of women were murdered at the hands of their partner. These figures are

For years, many healthcare organizations tended to be skeptical and resistant (if not outright hostile) to the idea of storing their data, particularly protected health

Many of us say that we’re concerned about protecting our privacy and personal data online. And yet, our actions say otherwise. Recent research suggests that even

Fixing a “typo” in a law governing domestic surveillance is the top priority for the bureau this year, FBI Director James B. Comey has said.

With IT budgets on the rise, and the average company spending 5% of its revenues on IT, according to one study, billions of dollars are
