
What to Do When You Suspect a Data Breach: Your First Step Guide
Once you suspect a data breach, try to stay composed and evaluate the circumstance. It’s essential to act quickly to minimize any potential damage or

Once you suspect a data breach, try to stay composed and evaluate the circumstance. It’s essential to act quickly to minimize any potential damage or

Telecoms fraud is a prevalent and ever-evolving issue that affects both business and individual customers in the telecommunications industry. It encompasses a range of fraudulent

As more organizations engage in it to safeguard themselves against online attacks, artificial intelligence (AI) is quickly emerging as a critical cybersecurity tool. This is

Tips and tricks for securing data when migrating to the cloud Find out how you can have a safe and secure transition to the cloud.

Without a doubt, the biggest threat to an organization’s cybersecurity is its people. Either willingly through an insider attack or unwittingly through social engineering, most
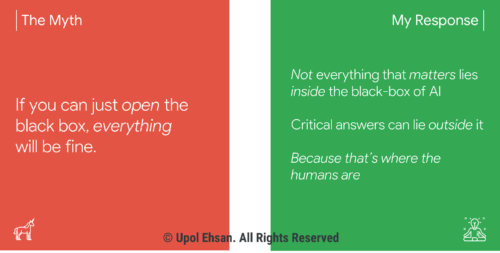
“So, the machine has high accuracy and explains its decisions, but we still don’t have engagement with our users?” I asked seeking clarification on a

Sometimes an AI-based system can’t decipher the physical world with a sufficient degree of accuracy and the option of just adding more data isn’t possible.

Wiz launched a community-driven database to improve reporting and transparency for cloud vulnerabilities, which are sometimes swept under the rug. Motivated by the troublesome disparities
Ransomware is not a new attack vector. In fact, the first malware of its kind appeared more than 30 years ago and was distributed via

I work with IT and business leaders in the auto industry every day, and they’re constantly thinking about what’s next, what new services they’ll need
First off, we should ask: What does multi-cloud mean and how does it differ from the typical cloud approach? In brief, a multi-cloud is a

With cloud computing growing at a phenomenal rate across the world, shifts in consumer behavior towards digital services are resulting in evolutionary changes for the
